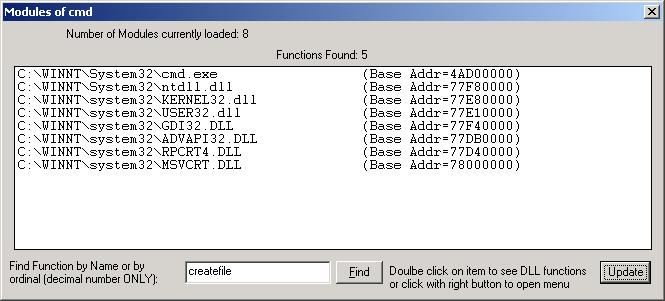
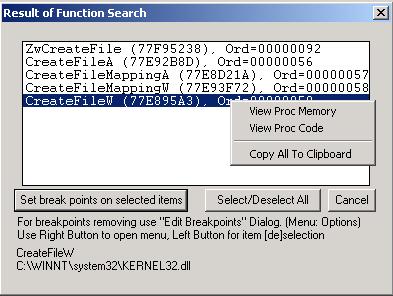
Socket Spy is the utility which permits you to trap a lot of system calls and check behavior of Windows Application, yours or third party. It works only in NT/2000/XP Window environment and does not works under 95/98/ME. By default it set number of breakpoint on selected system functions from wsock32.dll, icmp.dll (iphlpapi.dll), snmpapi.dll, netapi.dll, mpr.dll and kernel32.dll. These default breakpoints are named as soft breakpoint. When debugged application meets soft breakpoint it sends debug event to Socket Spy and Socket Spy proceeds soft breakpoints by dumping information to user terminal (short form) or save it to log files.
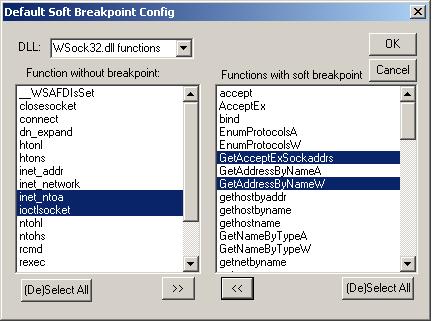
As mentioned above Socket Spy is a debugger which proceed breakpoints set on some system functions. Initial versions of Socket Spy worked only with WSock32.dll functions, but later additional functions from other DLLs were included. Besides additional features were developed, such as setting hard breakpoints (where debugged application stops execution) on any system function, view all DLL modules and their functions, read/write operation with debugged process memory, disassembler of debugged binary code and others. If you works with Numega’s Boundschecker, probably you notice that process of execution is slow down. It happens because Boundschecker spends time for breakpoints proceedings. In the same way execution of debugged process under Socket Spy will be slower as usual, but removing unnecessary soft breakpoints from default soft breakpoint list will give you possibility to proceed only functions you need and make execution faster and user terminal dump and log file shorter. It should be done before you select process for debugging. From Options menu select Default Breakpoint List Config and the following modal dialog will open:
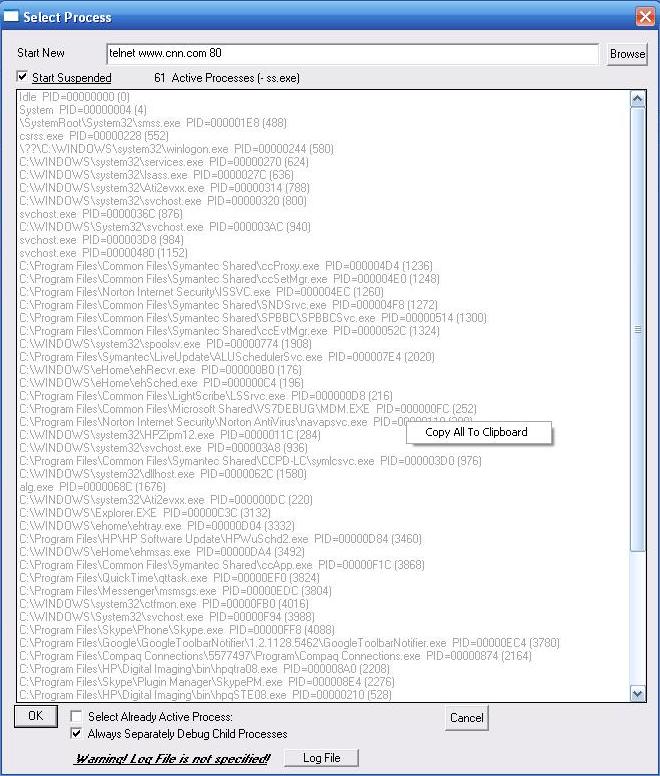
Process Selection.
Currently everything is ready to selected debugged
process. Click on Select Process button or use File Select Process
menu and following modal dialog opens
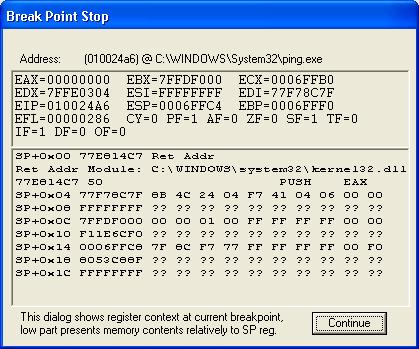

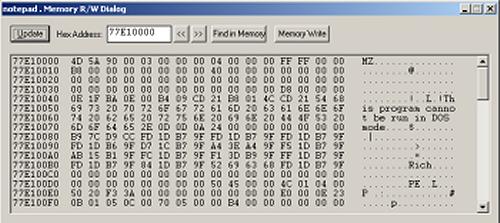
Other screen short examples
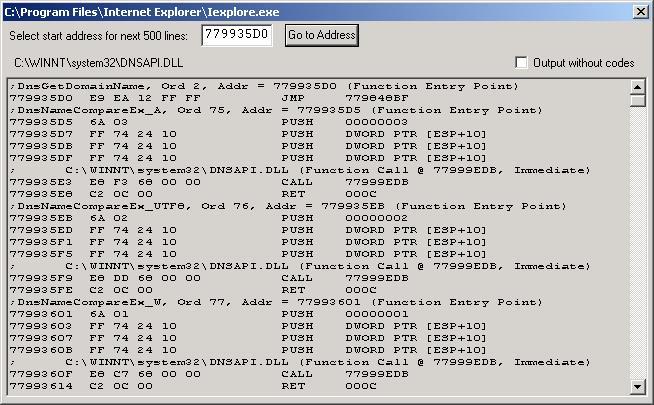
Disassembler:
For more detail download SS.ZIP file, unzip it and read MANUAL.DOC file.